Summer 2022. Maria tells me about a microfiction contest. Naïve me takes the bait. “A story in 400 words or fewer?! How could you even...” I trailed off. My first attempt was “The Wind,” a sordid Hitchcock & Bradbury meet mutated-haiku tale set on an idylic college campus. It’s particularly terse, fewer than 300 words. … Continue reading The Chill Bill Contingency
Category: Dan Dreifort
Dan Dreifort articles. Seemingly about him, by him. Who publishes this stuff? Oh yeah: Dan Dreifort.
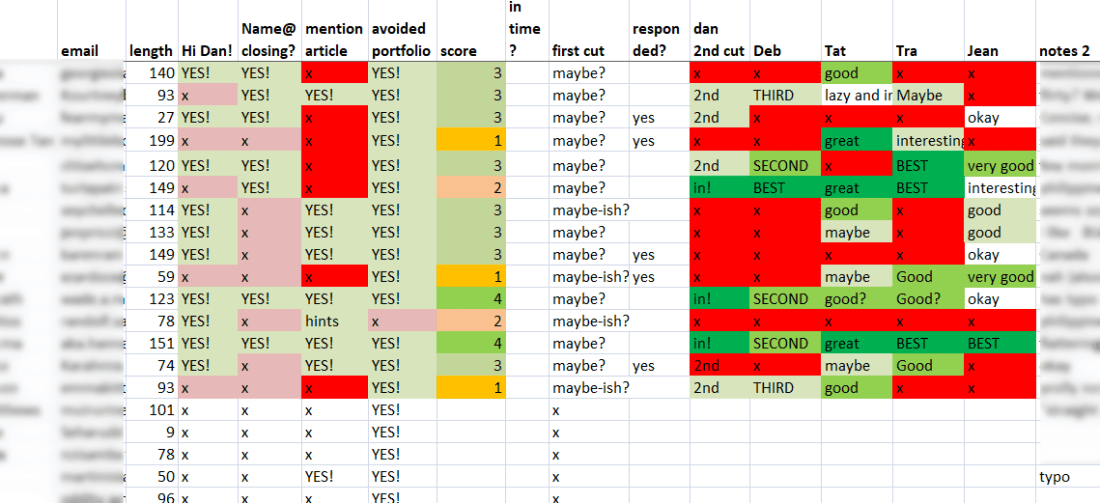
A time-themed letter to SEO-writer finalists
This is an installment in a series of riveting pre-hiring, screening, and response communications, mostly tailored to the SEO world. They’re mainly for my future use, but some people (and Google) seem to like them too. And why wouldn’t they? This is exciting stuff! /s If you're reading this after initial publication, please note that … Continue reading A time-themed letter to SEO-writer finalists
Mass-Rejection Letter to Aspiring Writers + Unsolicited Advice
Regular readers (a few “friends” held at gunpoint) are no doubt familiar with my pieces about hiring SEO writers and optimizing the applicant screening process. “Fans” of those articles might appreciate this companion piece. I'm in the midst of a round of hiring. (Future-Dan is also using this article for those who didn't make the … Continue reading Mass-Rejection Letter to Aspiring Writers + Unsolicited Advice
Qualified Leads: Who’s visiting our website?
Whether you call it lead intelligence, customer identification, big-data visitor tracking, or some other slightly misleading, newfangled web marketing forensics buzzword, it's sometimes useful to know exactly who's visiting your website.
SEO Writer Onboarding
This guide is intended for those thinking about writing and editing with _fiicient, but you might find it interesting for other reasons too. …Or not. Every search engine optimization minion knows content is king. I’ve been doing this SEO thing for others since 2004; time for an article about starting a relationship with a new writer.
Ned Beatty Interview
In May 2001 I interviewed Ned Beatty at the 28th Athens (OH) International Film Festival. Ned passed away a few days ago. This interview, originally published in the Athens News, was read by many hundreds of or perhaps a few thousand people. Buried on one of my crusty, dusty websites for decades, it's time to … Continue reading Ned Beatty Interview
I’m paying you to ‘do SEO’ …What else can we do?
File this one under: Things SEO clients ask often enough to warrant a blog-post answer. Wow! Dan's hooking you up with the SEO secret sauce? Lucky you! Can we do anything else to make his job easier improve your organic Google visibility? Yes. Me: "What picture should I use?" Wife: "Lucy in glasses; he looks … Continue reading I’m paying you to ‘do SEO’ …What else can we do?
Dan Dreifort Today: Reflections on Sketching 2.0
I used to love drawing. My parents stuck me in a couple art classes at the Cleveland Museum of Art when I was a wee one. I'm thankful for it. I drew semi-regularly for almost a decade, until I discovered playing the guitar, chicks, and bangs. After that, my scribbling diminished to almost nothing for … Continue reading Dan Dreifort Today: Reflections on Sketching 2.0
Answered: How do I get an image next to my site’s Google SERP listing?
Updated for 2024: Astute searchers have increasingly noted Google SERPs adding images next to regular organic listings, especially in mobile search. Here are two examples: You should get an image next to your mobile Google results, too! Business image thumbnails like these are one example of what Google calls SERP enhancements. It’s important to remember … Continue reading Answered: How do I get an image next to my site’s Google SERP listing?
Redirector Browser Extension Takes You Where You Want to Go
AT&T just installed fiber to my house. It's fast. I get a steady 949 Mbps up and down. I had no complaints about the 160 Mbps/14 Mbps I was getting from Cox, but my inner geek couldn't say no to faster-for-the-same-price. The install was pretty smooth, but during the bumps, I would type nonsense URLs … Continue reading Redirector Browser Extension Takes You Where You Want to Go